- Wednesday
- April 24th, 2024
- Submit Post

[ad_1] American clean energy automotive firm Tesla reported a 9% drop in revenue in the first quarter of 2024, the steepest year-over-year decline for the company since 2012. Its revenue dropped to $21.30 billion in Q124 as compared to $23.33...

[ad_1] Major General Aharon Haliva acknowledged failure to warn of the October 7 attack.More than six months after Hamas carried out an assault on southern Israel, the Israeli military intelligence chief has resigned. In his resignation letter, Major General Aharon...

[ad_1] View gallery Image Credit: Getty Images Halle Bailey is powering through a “severe” period of postpartum depressing following the birth of her baby boy, Halo. The 24-year-old Little Mermaid star got candid in a recent Snapchat video about her...

[ad_1] NewsFeedPro-Palestine protests are growing in momentum, while also being accused of threatening the safety of students at US university campuses.Published On 23 Apr 202423 Apr 2024 [ad_2] Crime Today News | World Source | Powered by Yes Mom Hosting

[ad_1] The second day of arguments in former United States President Donald Trump’s New York hush money trial has concluded with the prosecution’s questioning of former tabloid publisher David Pecker dominating much of the proceedings. Trump has been charged with...

[ad_1] Tamannaah Bhatia and Raashii Khanna's Aranmanai 4 has a new release date. While the movie was initially scheduled to release on April 26, it is not hitting the theatres on May 3. The makers took to a social media...
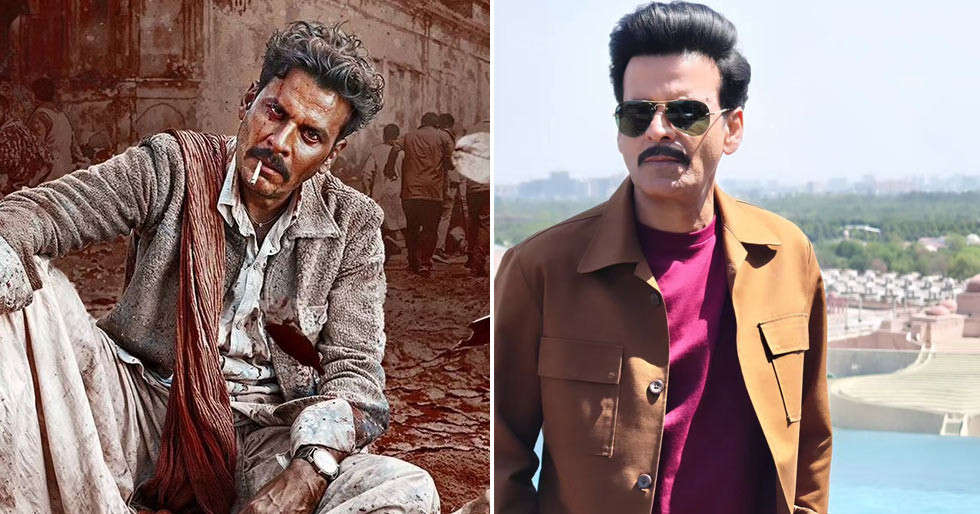
[ad_1] Bollywood actor Manoj Bajpayee is celebrating his 55th birthday today and on this occasion the makers of his upcoming film Bhaiyya Ji, have given us a glimpse of a song from the film. The song is titled Baagh Ka...

[ad_1] View gallery Image Credit: Michael Yarish/Netflix Actors almost always need a stunt double, and Candace Cameron Bure proved this while recalling a nearly fatal incident while working on the set of Fuller House. The 48-year-old actress sat down with...

[ad_1] NewsFeedUNRWA head Philippe Lazzarini told Al Jazeera that attacks on his agency are part of an effort to strip Palestinians of their refugee status. He added his agency is surviving ‘hand-to-mouth’ but can function at least through June.Published On...
 Loading posts...
Loading posts...  All posts loaded - Crime Today News
All posts loaded - Crime Today News
No more posts

